Remote Device Management Software
Remote device management (RDM) gives remote users access to web applications and workstations.
Remote Device Management
IT administrators can use AuthX Remote Device Management software to manage devices, troubleshoot issues, manage apps, and restrict access to unwanted data from a single platform. The Remote device management features of AuthX allow remote control, monitoring, and regulation of mobile devices, workstations, and tablets in an organization.
Manage Devices and Authenticate Users From Anywhere and at Any Time
Remote monitoring management is one of the top priorities for developing a secure enterprise workforce. AuthX Reports and Alerts provide detailed information on which devices have been assigned to the user and what application access they have.
Respond to Emerging Threats or Risks
AuthX enables network administrators to secure their architecture by disabling desktop access on specific devices, whether it’s a lost laptop or an insider threat. The built-in AuthX program safeguards your computer against malware attacks.
Increase Device Controls to Enable Zero Trust
Worry less about BYOD or remote access because AuthX’s remote device management platform extends security all the way down to the end user device. Access to organizational resources can be easily disabled from a single central management portal.
Frequently Asked Questions
Is it possible to use a single account to manage multiple mobile devices?
AuthX’s remote device management system is a web-based interface that allows you to manage and control multiple devices from a single account.
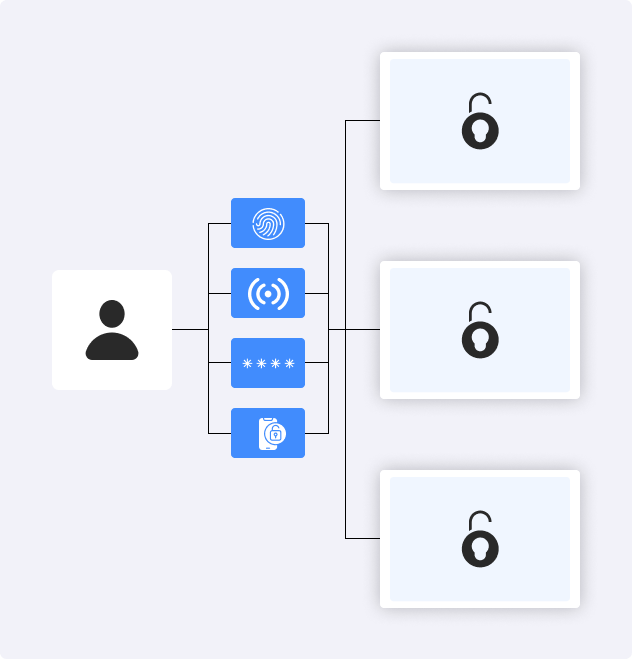
What are the most secure ways to authenticate your devices in a remote environment?
AuthX provides a variety of secure authentication methods, including biometric authentication. Using mobile phones, you can authenticate by sending an OTP to your registered mobile number, receiving a push notification, or using RFID.
How can we avoid phishing attacks when using our devices in remote locations?
The strong security system of AuthX’s remote access device management solutions protects users and their devices from cyberattacks by preventing them from accessing malicious online apps or emails.
What is the process for monitoring user access to devices and producing reports?
Using the AuthX Reports and Analysis feature, generate reports for all user identities and user access over device management.
