Zero Trust: Identity-Centric Security

Why Does Traditional Security Fall Short?
Perimeter-based security is no longer sufficient. Both external and internal sources may pose a threat to the security of your system. Businesses using legacy protections have to deal with:
Credential Theft
Password theft continues to be the primary cause of breaches.
Insider Theft
Employees and contractors may intentionally or accidentally disclose confidential information.
Lateral Movement
Once an intrusion has occurred, attackers move undetected across systems.
Cloud & Remote Risks
As attack surfaces increase, so does the difficulty of securing access.
Regulatory Compliance Gaps
Strict access controls are required by laws like HIPAA, PCI-DSS, and NIST.
Benefits of Zero Trust Security Without Complexity
Zero Trust strengthens security without slowing you down—keeping access seamless and protection airtight.
Lateral Movement
Once an intrusion has occurred, attackers move undetected across systems.
Least Privilege Access
Limit access strictly to what users need, reducing blast radius and preventing unnecessary exposure.
Device Trust Assurance
Allow access only from devices that meet defined security posture requirements.
Real-time Threat Detection
Detect and block suspicious behavior before it escalates into lateral movement or data loss.
Seamless Integration
Apply Zero Trust policies consistently across cloud, on-prem, and hybrid environments without breaking workflows.
Proactive Fraud Prevention
Detect anomalies early and prevent unauthorized access before security breaches happen.
Why Choose AuthX for Zero Trust?
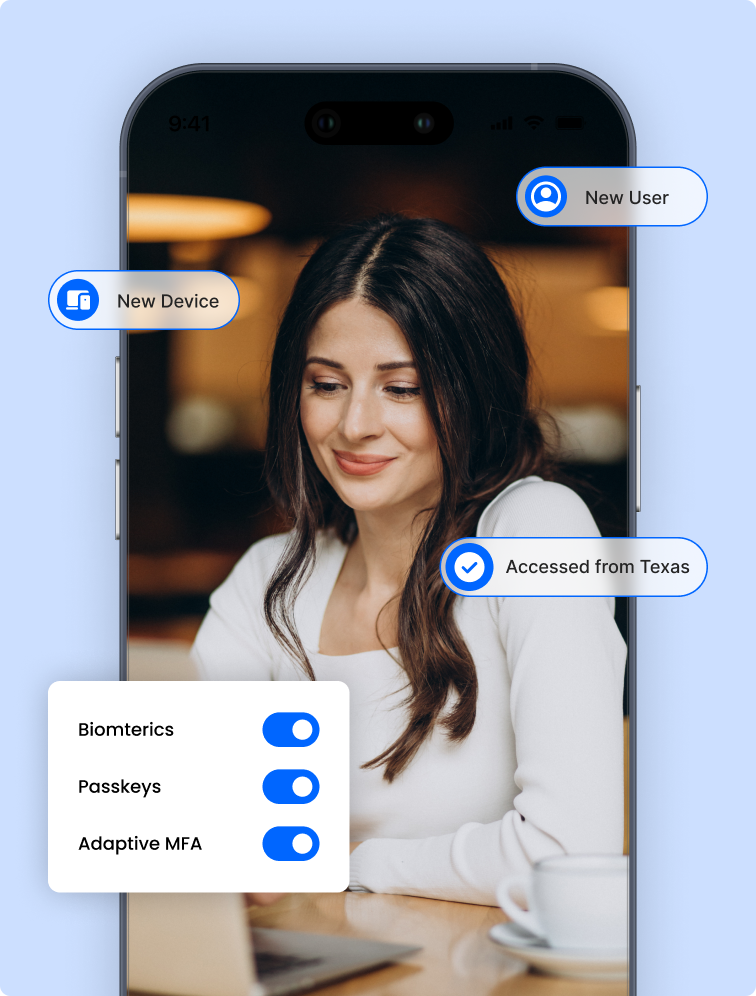
Identity-Centric Security
Use AuthX’s biometrics, adaptive MFA, and risk-based policies to authenticate users.
Comprehensive Device Security
Enforce security upgrades and verify devices before allowing access to ensure complete device security.
Continuous Monitoring
Detect suspicious behavior and respond to risks automatically.
Granular Access Controls
To reduce insider threats, employ least privileged access.
Frictionless User Experience
Secure authentication that does not disrupt normal activities.
Regulatory Compliance
Follow industry standards by adopting rigorous access controls and identity verification.
AuthX Zero Trust in Action: A Comprehensive Defense Strategy for Preventing Cyberthreats
Alert Triggered
Unauthorized access attempt detected based on identity, device, or behavioral risk.
Isolation Protocol Activated
Risky users, devices, or sessions are isolated automatically.
Access Revoked
Access is revoked immediately to prevent lateral movement or data exposure.
Continuous Monitoring
User sessions are monitored throughout their lifecycle, not just at login.
Adaptive Security Measures
Additional authentication is enforced when risk thresholds are exceeded.
Incident Response & Remediation
Logs and access events are analyzed to refine policies and prevent recurrence.
Use Cases by Industries
Secure Every Sector with Granular Access Control
Healthcare
Protect EHRs, prescription systems, and patient data with biometric and risk-based authentication.
Finanace
Secure transactions and customer accounts from fraud and identity theft.
Education
Safeguard student records, learning platforms, and faculty systems.
Manufacturing
Manage access to IoT devices, operational tools, and supply chain networks.
Retail
Prevent unauthorized access to POS systems, inventory management software, and CRM platforms
How to Implement Zero Trust with AuthX?
01 Assess Security Needs
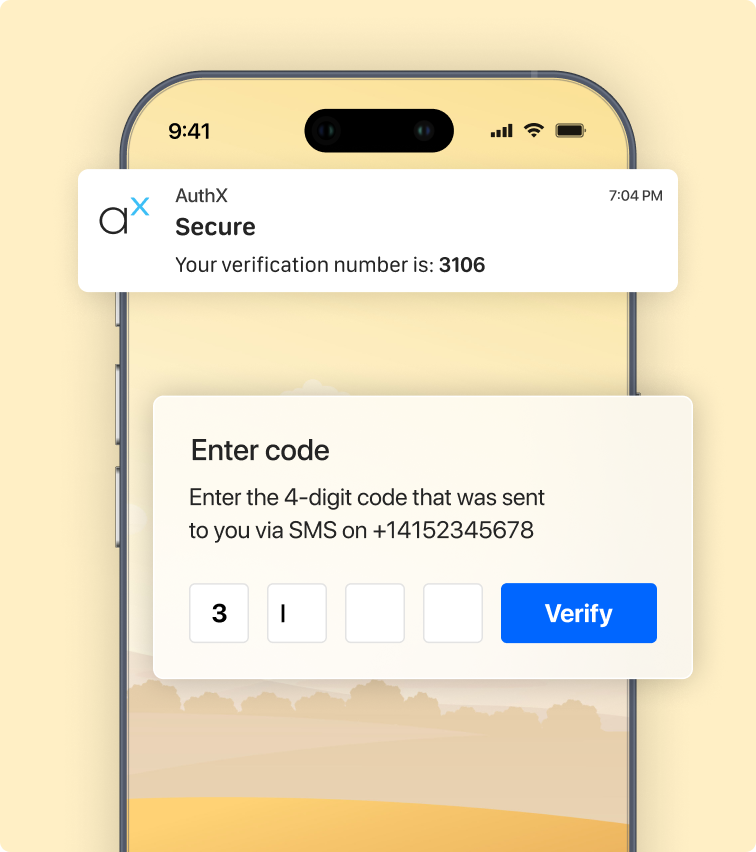
A customer signs in to their bank’s portal using a passkey stored securely on their mobile device; no passwords are involved.


02 Define Access Policies
Enforce MFA, device trust, and least-privilege access.
03 Enable Authentication Methods
Deploy biometrics, passkeys, smart cards, or mobile push.


04 Monitor & Adapt
Use real-time analytics to detect threats and adjust policies.
05 Deploy & Train Users
Roll out Zero Trust workflows with minimal disruption.

06 Optimize Continuously
Evolve controls as environments and threats change.
